Security/Sandbox: Difference between revisions
Haftandilian (talk | contribs) (Add mention of the socket process for Mac.) |
(→Content: Update windows content sandbox levels) |
||
| (13 intermediate revisions by 3 users not shown) | |||
| Line 9: | Line 9: | ||
* [https://wiki.mozilla.org/Security/Sandbox/Specifics Platform Specifics] | * [https://wiki.mozilla.org/Security/Sandbox/Specifics Platform Specifics] | ||
* [https://wiki.mozilla.org/Security/Sandbox/Deny_Filesystem_Access File Restrictions Bug Research] | * [https://wiki.mozilla.org/Security/Sandbox/Deny_Filesystem_Access File Restrictions Bug Research] | ||
* [https://wiki.mozilla.org/Security/Sandbox/Hardening Hardening Research] | * [https://wiki.mozilla.org/Security/Sandbox/Hardening Hardening Research] | ||
* [https://wiki.mozilla.org/Security/Sandbox/Process_model Process Model] | * [https://wiki.mozilla.org/Security/Sandbox/Process_model Process Model] | ||
| Line 37: | Line 36: | ||
|- | |- | ||
|colspan="1"| [https://dxr.mozilla.org/mozilla-central/search?q=SetSecurityLevelForGPUProcess&redirect=true Windows (compositor)] | |colspan="1"| [https://dxr.mozilla.org/mozilla-central/search?q=SetSecurityLevelForGPUProcess&redirect=true Windows (compositor)] | ||
|style='text-align:center;' colspan="2"|Level | |style='text-align:center;' colspan="2"|Level 1 | ||
|style='text-align:center;' colspan="1"| | |style='text-align:center;' colspan="1"|Level 1 | ||
|style='text-align:center;' colspan="1"| | |style='text-align:center;' colspan="1"| | ||
|style='text-align:center;' colspan="1"|Level 1 | |||
|style='text-align:center;' colspan="1"| | |style='text-align:center;' colspan="1"| | ||
|- | |- | ||
| Line 54: | Line 53: | ||
|style='text-align:center;' colspan="1"|Level 1 | |style='text-align:center;' colspan="1"|Level 1 | ||
|style='text-align:center;' colspan="1"|Fx75 | |style='text-align:center;' colspan="1"|Fx75 | ||
|- | |- | ||
| [https://searchfox.org/mozilla-central/source/security/sandbox/mac/SandboxPolicyContent.h OSX (content)] | | [https://searchfox.org/mozilla-central/source/security/sandbox/mac/SandboxPolicyContent.h OSX (content)] | ||
| Line 81: | Line 75: | ||
|style='text-align:center;' colspan="2"|disabled | |style='text-align:center;' colspan="2"|disabled | ||
|style='text-align:center;' colspan="2"|disabled | |style='text-align:center;' colspan="2"|disabled | ||
|- | |- | ||
| [https://dxr.mozilla.org/mozilla-central/search?q=class+ContentSandboxPolicy&redirect=true&case=true Linux (content)] | | [https://dxr.mozilla.org/mozilla-central/search?q=class+ContentSandboxPolicy&redirect=true&case=true Linux (content)] | ||
| Line 101: | Line 90: | ||
A 'level' value reflects unique sandbox security settings for each platform and process. Most processes only have two "active" levels, the current setting and a lower (previous released) setting. Level settings other than these two values carry no guarantee of altering security behavior, level settings are primarily a release rollout debugging feature. | A 'level' value reflects unique sandbox security settings for each platform and process. Most processes only have two "active" levels, the current setting and a lower (previous released) setting. Level settings other than these two values carry no guarantee of altering security behavior, level settings are primarily a release rollout debugging feature. | ||
== Windows == | == Windows == | ||
| Line 112: | Line 99: | ||
{| class="wikitable" | {| class="wikitable" | ||
|- | |- | ||
! Sandbox Feature !! Level | ! Sandbox Feature !! Level 6 !! Level 7 (Release) !! Level 8 (Nightly) | ||
|- | |- | ||
| Job Level || | | Job Level || JOB_LOCKDOWN || JOB_LOCKDOWN || JOB_LOCKDOWN | ||
|- | |- | ||
| Access Token Level || | | Access Token Level || USER_LIMITED || USER_LIMITED || '''''USER_RESTRICTED''''' | ||
|- | |- | ||
| Alternate Desktop || | | Alternate Desktop || YES || YES || YES | ||
|- | |- | ||
| Alternate Windows Station || | | Alternate Windows Station || YES || YES || YES | ||
|- | |- | ||
| Initial Integrity Level || | | Initial Integrity Level || INTEGRITY_LEVEL_LOW || INTEGRITY_LEVEL_LOW || INTEGRITY_LEVEL_LOW | ||
|- | |- | ||
| Delayed Integrity Level | | Delayed Integrity Level || INTEGRITY_LEVEL_LOW || '''''INTEGRITY_LEVEL_UNTRUSTED''''' || INTEGRITY_LEVEL_UNTRUSTED | ||
|| | |||
|- | |- | ||
| | | Mitigations | ||
|| | || | ||
MITIGATION_BOTTOM_UP_ASLR<br> | MITIGATION_BOTTOM_UP_ASLR<br> | ||
| Line 178: | Line 122: | ||
MITIGATION_EXTENSION_POINT_DISABLE<br> | MITIGATION_EXTENSION_POINT_DISABLE<br> | ||
MITIGATION_IMAGE_LOAD_NO_REMOTE<br> | MITIGATION_IMAGE_LOAD_NO_REMOTE<br> | ||
MITIGATION_IMAGE_LOAD_NO_LOW_LABEL | MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | ||
MITIGATION_IMAGE_LOAD_PREFER_SYS32<br> | |||
MITIGATION_CONTROL_FLOW_GUARD_DISABLE<br> | |||
MITIGATION_WIN32K_DISABLE<br> | |||
Locked Down Default DACL | |||
|| | || | ||
MITIGATION_BOTTOM_UP_ASLR<br> | MITIGATION_BOTTOM_UP_ASLR<br> | ||
| Line 188: | Line 136: | ||
MITIGATION_IMAGE_LOAD_NO_REMOTE<br> | MITIGATION_IMAGE_LOAD_NO_REMOTE<br> | ||
MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | ||
MITIGATION_IMAGE_LOAD_PREFER_SYS32 | MITIGATION_IMAGE_LOAD_PREFER_SYS32<br> | ||
MITIGATION_CONTROL_FLOW_GUARD_DISABLE<br> | |||
MITIGATION_WIN32K_DISABLE<br> | |||
Locked Down Default DACL | |||
|| | || | ||
MITIGATION_BOTTOM_UP_ASLR<br> | MITIGATION_BOTTOM_UP_ASLR<br> | ||
| Line 199: | Line 150: | ||
MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | ||
MITIGATION_IMAGE_LOAD_PREFER_SYS32<br> | MITIGATION_IMAGE_LOAD_PREFER_SYS32<br> | ||
MITIGATION_CONTROL_FLOW_GUARD_DISABLE<br> | |||
MITIGATION_WIN32K_DISABLE<br> | |||
Locked Down Default DACL | Locked Down Default DACL | ||
|- | |- | ||
| Delayed Mitigations | | Delayed Mitigations | ||
|| | || | ||
MITIGATION_STRICT_HANDLE_CHECKS<br> | MITIGATION_STRICT_HANDLE_CHECKS<br> | ||
| Line 217: | Line 168: | ||
[http://mxr.mozilla.org/mozilla-central/source/security/sandbox/chromium/sandbox/win/src/security_level.h Windows Feature Header] | [http://mxr.mozilla.org/mozilla-central/source/security/sandbox/chromium/sandbox/win/src/security_level.h Windows Feature Header] | ||
=== Gecko Media Plugin === | === Gecko Media Plugin (GMP) === | ||
{| class="wikitable" | {| class="wikitable" | ||
| Line 238: | Line 189: | ||
MITIGATION_HEAP_TERMINATE<br> | MITIGATION_HEAP_TERMINATE<br> | ||
MITIGATION_SEHOP<br> | MITIGATION_SEHOP<br> | ||
MITIGATION_EXTENSION_POINT_DISABLE<br> | |||
MITIGATION_DEP_NO_ATL_THUNK<br> | MITIGATION_DEP_NO_ATL_THUNK<br> | ||
MITIGATION_DEP | MITIGATION_DEP<br> | ||
MITIGATION_NONSYSTEM_FONT_DISABLE<br> | |||
MITIGATION_IMAGE_LOAD_NO_REMOTE<br> | |||
MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | |||
MITIGATION_CET_COMPAT_MODE<br> | |||
Locked Down Default DACL | |||
|- | |- | ||
| Delayed Mitigations | | Delayed Mitigations | ||
| Line 249: | Line 206: | ||
[1] depends on the media plugin | [1] depends on the media plugin | ||
=== | === Remote Data Decoder (RDD) === | ||
{| class="wikitable" | {| class="wikitable" | ||
| Line 255: | Line 212: | ||
! Sandbox Feature !! Level | ! Sandbox Feature !! Level | ||
|- | |- | ||
| Job Level || | | Job Level || JOB_LOCKDOWN | ||
|- | |- | ||
| Access Token Level || | | Access Token Level || USER_LIMITED | ||
|- | |- | ||
| Initial Integrity Level || INTEGRITY_LEVEL_LOW | | Initial Integrity Level || INTEGRITY_LEVEL_LOW | ||
| Line 263: | Line 220: | ||
| Delayed Integrity Level || INTEGRITY_LEVEL_LOW | | Delayed Integrity Level || INTEGRITY_LEVEL_LOW | ||
|- | |- | ||
| Alternate desktop || | | Alternate desktop || yes | ||
|- | |- | ||
| Mitigations | | Mitigations | ||
| Line 270: | Line 227: | ||
MITIGATION_HEAP_TERMINATE<br> | MITIGATION_HEAP_TERMINATE<br> | ||
MITIGATION_SEHOP<br> | MITIGATION_SEHOP<br> | ||
MITIGATION_EXTENSION_POINT_DISABLE<br> | |||
MITIGATION_DEP_NO_ATL_THUNK<br> | MITIGATION_DEP_NO_ATL_THUNK<br> | ||
MITIGATION_DEP | MITIGATION_DEP<br> | ||
MITIGATION_NONSYSTEM_FONT_DISABLE<br> | |||
MITIGATION_IMAGE_LOAD_NO_REMOTE<br> | |||
MITIGATION_IMAGE_LOAD_NO_LOW_LABEL<br> | |||
MITIGATION_IMAGE_LOAD_PREFER_SYS32<br> | |||
MITIGATION_CET_COMPAT_MODE<br> | |||
Locked Down Default DACL | |||
|- | |- | ||
| Delayed Mitigations | | Delayed Mitigations | ||
|| | || | ||
MITIGATION_STRICT_HANDLE_CHECKS<br> | |||
MITIGATION_DYNAMIC_CODE_DISABLE<br> | |||
MITIGATION_DLL_SEARCH_ORDER<br> | |||
MITIGATION_FORCE_MS_SIGNED_BINS | |||
|} | |} | ||
| Line 300: | Line 268: | ||
The socket process policy is defined in [https://searchfox.org/mozilla-central/source/security/sandbox/mac/SandboxPolicySocket.h SandboxPolicySocket.h]. At this time (May 2020), the socket process sandbox is only used on the Nightly channel and only for WebRTC networking. | The socket process policy is defined in [https://searchfox.org/mozilla-central/source/security/sandbox/mac/SandboxPolicySocket.h SandboxPolicySocket.h]. At this time (May 2020), the socket process sandbox is only used on the Nightly channel and only for WebRTC networking. | ||
== Linux == | == Linux == | ||
| Line 329: | Line 293: | ||
* Everything from level 1-3 | * Everything from level 1-3 | ||
* Network access including local sockets | * Network access including local sockets | ||
* System V IPC | * System V IPC | ||
** Unless fgxlrx or VirtualGL is in use | ** Unless fgxlrx or VirtualGL is in use | ||
| Line 371: | Line 334: | ||
|- | |- | ||
| Windows NPAPI Plugin || numerical || dom.ipc.plugins.sandbox-level.default<br>dom.ipc.plugins.sandbox-level.<plugintype> | | Windows NPAPI Plugin || numerical || dom.ipc.plugins.sandbox-level.default<br>dom.ipc.plugins.sandbox-level.<plugintype> | ||
|- | |- | ||
| Compositor || numerical || security.sandbox.gpu.level | | Compositor || numerical || security.sandbox.gpu.level | ||
| Line 426: | Line 387: | ||
# Launch the OS X Console app (/Applications/Utilities/Console.app) and filter on "plugin-container". | # Launch the OS X Console app (/Applications/Utilities/Console.app) and filter on "plugin-container". | ||
# Either set the pref '''security.sandbox.logging.enabled=true''' and restart the browser OR launch the browser with the '''MOZ_SANDBOX_LOGGING''' environment variable set | # Either set the pref '''security.sandbox.logging.enabled=true''' and restart the browser OR launch the browser with the '''MOZ_SANDBOX_LOGGING''' environment variable set. | ||
=== Linux specific Sandbox Logging === | === Linux specific Sandbox Logging === | ||
| Line 457: | Line 415: | ||
|Disable GPU process sandbox | |Disable GPU process sandbox | ||
|Windows | |Windows | ||
|- | |||
|MOZ_DISABLE_RDD_SANDBOX | |||
|Disable Data Decoder process sandbox | |||
|All | |||
|- | |||
|MOZ_DISABLE_SOCKET_PROCESS_SANDBOX | |||
|Disable Socket Process process sandbox | |||
|All | |||
|} | |} | ||
| Line 503: | Line 469: | ||
* webrtc specific sandboxing bugs: https://is.gd/c5bAe6 | * webrtc specific sandboxing bugs: https://is.gd/c5bAe6 | ||
** sb tracking + 'webrtc' | ** sb tracking + 'webrtc' | ||
= Roadmap = | |||
==2020 H1 - Main work focus== | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1464032 Remote Canvas Drawing operations], | |||
** Prerequisite for win32k.sys lockdown. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1381938 Remote Form widget drawing], | |||
** Prerequisite for win32k.sys lockdown. | |||
** Follow-ups in [https://bugzilla.mozilla.org/show_bug.cgi?id=1615105 Bug for defaulting it on] | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1642621 Remote WebGL drawing], | |||
** See also [https://bugzilla.mozilla.org/show_bug.cgi?id=1632249 Out-of-process WebGL compositing]. | |||
** Follow-ups in [https://bugzilla.mozilla.org/show_bug.cgi?id=1642621 Make it shippable bug]. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1347710 Sandbox the GPU Process]. | |||
** Stalled on non-reproducible [https://bugzilla.mozilla.org/show_bug.cgi?id=1630860 field issues]. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1400317 Remote Look and Feel + Theming]. | |||
** Prerequisite for win32k.sys lockdown. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1550900 Shared memory with read-only and read/write mode]. | |||
** Security and memory usage win. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1440203 Use memfd_create for shared memory]. | |||
** Performance win and would solve many issues with people running into problems with the default docker/kubernetes configurations that only give a tiny amount of shared memory. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1620118 Enable further telemetry for third-party process injection]. | |||
==2020 H2 - Main work focus== | |||
* Carry-over of win32k.sys lockdown prerequisites from 2020 H1. | |||
* Carry-over of stalled GPU sandboxing work. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1381019 Remaining win32k.sys blockers]. | |||
* [https://bugzilla.mozilla.org/show_bug.cgi?id=1620114 Enable CIG in RDD]. | |||
** Investigate/experiment with feasibility of shipping CIG in content. | |||
= Communication = | = Communication = | ||
| Line 509: | Line 503: | ||
| Weekly Team Meeting | | Weekly Team Meeting | ||
|| Thursday at 8:00am PT | || Thursday at 8:00am PT | ||
* | * Zoom: By invitation, ask gcp@mozilla.com | ||
* [https://wiki.mozilla.org/Security/Sandbox/Meeting_Notes Meeting Notes Archive] | * [https://wiki.mozilla.org/Security/Sandbox/Meeting_Notes Meeting Notes Archive] | ||
|- | |- | ||
| | | Matrix | ||
|| | || | ||
* [ | * Server: chat.mozilla.org | ||
* Channel: [https://chat.mozilla.org/#/room/#hardening:mozilla.org #hardening] | |||
|- | |- | ||
|} | |} | ||
| Line 529: | Line 518: | ||
| Engineering Management | | Engineering Management | ||
|| | || | ||
* | * Gian-Carlo Pascutto (gcp) | ||
|- | |- | ||
| Project Management | | Project Management | ||
|| | || | ||
* | * N/A | ||
|- | |- | ||
| QA | | QA | ||
|| | || | ||
* | * N/A | ||
|- | |- | ||
| Development Team | | Development Team | ||
| Line 543: | Line 532: | ||
* Haik Aftandilian (haik) | * Haik Aftandilian (haik) | ||
* Jed Davis (jld) | * Jed Davis (jld) | ||
* | * Chris Martin (cmartin) | ||
* Bob Owen (bobowen) | * Bob Owen (bobowen) | ||
* David Parks (handyman) | * David Parks (handyman) | ||
| Line 551: | Line 540: | ||
= Repo Module Ownership = | = Repo Module Ownership = | ||
* [[Modules/Core#Sandboxing_-_Windows|Windows]] | * [[Modules/Core#Sandboxing_-_Windows|Windows]] | ||
* [[Modules/Core#Sandboxing_-_OSX|OSX]] | * [[Modules/Core#Sandboxing_-_OSX|OSX]] | ||
* [[Modules/Core#Sandboxing_- | * [[Modules/Core#Sandboxing_-_Linux|Linux]] | ||
= Links = | = Links = | ||
| Line 565: | Line 553: | ||
* [http://en.wikipedia.org/wiki/Google_Native_Client Native Client on Wikipedia] (Links to papers on Native Client's design and use of SFI, as well as papers on SFI itself.) | * [http://en.wikipedia.org/wiki/Google_Native_Client Native Client on Wikipedia] (Links to papers on Native Client's design and use of SFI, as well as papers on SFI itself.) | ||
* [https://msdn.microsoft.com/en-us/library/windows/desktop/ff966517%28v=vs.85%29.aspx?f=255&MSPPError=-2147217396 Features of Protected Mode in Internet Explorer] | * [https://msdn.microsoft.com/en-us/library/windows/desktop/ff966517%28v=vs.85%29.aspx?f=255&MSPPError=-2147217396 Features of Protected Mode in Internet Explorer] | ||
== B2G Archive == | == B2G Archive == | ||
| Line 575: | Line 560: | ||
B2G has always been “sandboxed” to some extent; every app/tab gets its own content process, which uses the Android security model: a separate uid per process, no group memberships, and kernel patches that require group membership for things like network access. But privilege escalation via kernel vulnerabilities is relatively common, so we also use the seccomp-bpf system call filter to reduce the attack surface that a compromised content process can directly access. | B2G has always been “sandboxed” to some extent; every app/tab gets its own content process, which uses the Android security model: a separate uid per process, no group memberships, and kernel patches that require group membership for things like network access. But privilege escalation via kernel vulnerabilities is relatively common, so we also use the seccomp-bpf system call filter to reduce the attack surface that a compromised content process can directly access. | ||
Latest revision as of 16:53, 11 October 2024
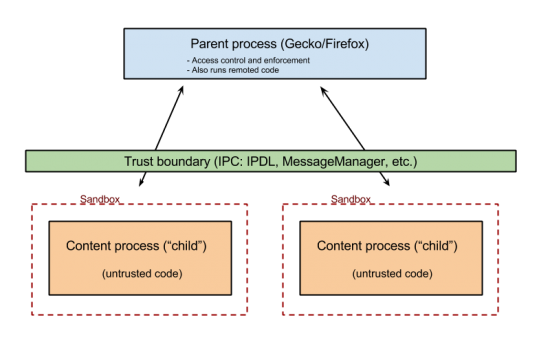
Overview
Security Sandboxing makes use of child processes as a security boundary. The process model, i.e. how Firefox is split into various processes and how these processes interact between each other is common to all platforms. For more information see the Electrolysis wiki page, and its sucessor, Project Fission. The security aspects of a sandboxed child process are implemented on a per-platform basis. See the Platform Specifics section below for more information.
Technical Docs
Current Status
| Sandbox | Trunk | Beta | Release | |||
|---|---|---|---|---|---|---|
| Level | Level | Version | Level | Version | ||
| Windows (content) | Level 6 | Level 6 | Fx76 | Level 6 | Fx76 | |
| Windows (compositor) | Level 1 | Level 1 | Level 1 | |||
| Windows (GMP) | enabled | enabled | enabled | |||
| Windows (Socket) | Level 1 | Level 1 | Fx75 | Level 1 | Fx75 | |
| OSX (content) | Level 3 | Level 3 | Fx56 | Level 3 | Fx56 | |
| OSX (GMP) | enabled | enabled | enabled | |||
| OSX (RDD) | enabled | enabled | enabled | |||
| OSX (Socket) | enabled | disabled | disabled | |||
| Linux (content) | Level 4 | Level 4 | Fx60 | Level 4 | Fx60 | |
| Linux (GMP) | enabled | enabled | enabled | |||
A 'level' value reflects unique sandbox security settings for each platform and process. Most processes only have two "active" levels, the current setting and a lower (previous released) setting. Level settings other than these two values carry no guarantee of altering security behavior, level settings are primarily a release rollout debugging feature.
Windows
Content
Sandbox security related setting are grouped together and associated with a security level. Lower level values indicate a less restrictive sandbox.
| Sandbox Feature | Level 6 | Level 7 (Release) | Level 8 (Nightly) |
|---|---|---|---|
| Job Level | JOB_LOCKDOWN | JOB_LOCKDOWN | JOB_LOCKDOWN |
| Access Token Level | USER_LIMITED | USER_LIMITED | USER_RESTRICTED |
| Alternate Desktop | YES | YES | YES |
| Alternate Windows Station | YES | YES | YES |
| Initial Integrity Level | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW |
| Delayed Integrity Level | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_UNTRUSTED | INTEGRITY_LEVEL_UNTRUSTED |
| Mitigations |
MITIGATION_BOTTOM_UP_ASLR |
MITIGATION_BOTTOM_UP_ASLR |
MITIGATION_BOTTOM_UP_ASLR |
| Delayed Mitigations |
MITIGATION_STRICT_HANDLE_CHECKS |
MITIGATION_STRICT_HANDLE_CHECKS |
MITIGATION_STRICT_HANDLE_CHECKS |
Gecko Media Plugin (GMP)
| Sandbox Feature | Level |
|---|---|
| Job Level | JOB_LOCKDOWN |
| Access Token Level | USER_LOCKDOWN, USER_RESTRICTED[1] |
| Initial Integrity Level | INTEGRITY_LEVEL_LOW |
| Delayed Integrity Level | INTEGRITY_LEVEL_UNTRUSTED |
| Alternate desktop | yes |
| Mitigations |
MITIGATION_BOTTOM_UP_ASLR |
| Delayed Mitigations |
MITIGATION_STRICT_HANDLE_CHECKS |
[1] depends on the media plugin
Remote Data Decoder (RDD)
| Sandbox Feature | Level |
|---|---|
| Job Level | JOB_LOCKDOWN |
| Access Token Level | USER_LIMITED |
| Initial Integrity Level | INTEGRITY_LEVEL_LOW |
| Delayed Integrity Level | INTEGRITY_LEVEL_LOW |
| Alternate desktop | yes |
| Mitigations |
MITIGATION_BOTTOM_UP_ASLR |
| Delayed Mitigations |
MITIGATION_STRICT_HANDLE_CHECKS |
OSX
Content Levels for Web and File Content Processes
Mac content processes use sandbox level 3. File content processes (for file:/// origins) also use level 3 with additional rules to allow read access to the filesystem. Levels 1 and 2 can still be enabled in about:config, but they are not supported and using them is not recommended. Different sandbox levels were used for testing and debugging during rollout of Mac sandboxing features, but they now are planned to be removed. Mac sandboxing uses a white list policy for all process types. Each policy begins with a statement to deny all access to system resources and then specifies the allowed resources. The level 3 sandbox allows file system read metadata access with full read access for specific system directories and some user directories, access to the microphone, access to various system services, windowserver, named sysctls and iokit properties, and other miscellaneous items. Work is ongoing to remove access to the microphone, windowserver, and other system services where possible. The sandbox blocks write access to all of the file system, read access to the profile directory (apart from the chrome and extensions subdirectories, read access to the home directory, inbound/outbound network I/O, exec, fork, printing, video input devices such as cameras. Older sandbox levels 1 and 2 are less restrictive. Mainly, level 2 allows file-read access to all of the filesystem except the ~/Library directory. Level 1 allows all file-read access. Level 1 restrictions are a subset of level 2. Level 2 restrictions are a subset of level 3.
The web and file content policy is defined in SandboxPolicyContent.h
Gecko Media Plugin Processes
The Gecko Media Plugins (GMP) policy is defined in SandboxPolicyGMP.h.
Remote Data Decoder Processes
The Remote Data Decoder (RDD) policy is defined in SandboxPolicyUtility.h.
Socket Process
The socket process policy is defined in SandboxPolicySocket.h. At this time (May 2020), the socket process sandbox is only used on the Nightly channel and only for WebRTC networking.
Linux
Content Levels
| Job Level | What's Blocked by the Sandbox? |
|---|---|
| Level 1 |
|
| Level 2 |
|
| Level 3 |
|
| Level 4 |
|
Content Rules
Gecko Media Plugin
Customization Settings
The Linux sandbox allows some amount of control over the sandbox policy through various about:config settings. These are meant to allow more non-standard configurations and exotic distributions to stay working - without compiling custom versions of Firefox - even if they can't be directly supported by the default configuration.
See Activity Logging for information on how to debug these scenarios.
security.sandbox.content.level
- See Content Levels above. Reducing this can help identify sandboxing as the cause of a problem, but you're better of trying the more fine grained permissions below.
security.sandbox.content.read_path_whitelist
security.sandbox.content.write_path_whitelist
- Comma-separated list of additional paths that the content process is allowed to read from or write to, respectively. To allow access to an entire directory tree (rather than just the directory itself), include a trailing / character.
security.sandbox.content.syscall_whitelist
- Comma-seperated list of additional system call numbers that should be allowed in the content process. These affect the seccomp-bpf filter.
Preferences
| Process Type | Preference Type | Preference |
|---|---|---|
| Content | numerical | security.sandbox.content.level |
| Windows NPAPI Plugin | numerical | dom.ipc.plugins.sandbox-level.default dom.ipc.plugins.sandbox-level.<plugintype> |
| Compositor | numerical | security.sandbox.gpu.level |
| Media | Embedded | N/A |
Note - Levels greater than the current default for a particular process type are not implemented.
File System Restrictions
Sandboxing enforces file system write and read restrictions for XUL based add-on content (frame and process) scripts. To avoid issues as sandboxing features roll out add-on authors should update their legacy add-on code today such that content scripts no longer attempt to read or write from restricted locations. Note these restrictions do not affect WebExtension content script or XUL add-on script running in the browser process.
File system access rules for content processes, reverse precedence:
| Location | Access Type | Restriction |
|---|---|---|
| file system | read/write | deny by default |
| install location | write | deny |
| install location | read | allow |
| system library locations | write | deny |
| system library locations | read | allow |
| profile/* | read/write | deny by default |
| profile/extensions | write | deny |
| profile/extensions | read | allow |
Debugging Features
Activity Logging
The following prefs control sandbox logging. On Windows, output is sent to the Browser Console when available, and to a developer console attached to the running browser process. On OSX, once enabled, violation log entries are visible in the Console.app (/Applications/Utilities/Console.app). On Linux, once enabled, violation log entries are logged on the command line console.
security.sandbox.logging.enabled (boolean)
security.sandbox.windows.log.stackTraceDepth (integer, Windows specific)
The following environment variables also triggers sandbox logging output:
MOZ_SANDBOX_LOGGING=1
OSX Specific Sandbox Logging
On Mac, sandbox violation logging is disabled by default. To enable logging,
- Launch the OS X Console app (/Applications/Utilities/Console.app) and filter on "plugin-container".
- Either set the pref security.sandbox.logging.enabled=true and restart the browser OR launch the browser with the MOZ_SANDBOX_LOGGING environment variable set.
Linux specific Sandbox Logging
The following environment variable triggers extra sandbox debugging output:
MOZ_SANDBOX_LOGGING=1
Environment variables
| ENVIRONMENT VARIABLE | DESCRIPTION | PLATFORM |
|---|---|---|
| MOZ_DISABLE_CONTENT_SANDBOX | Disables content process sandboxing for debugging purposes. | All |
| MOZ_DISABLE_GMP_SANDBOX | Disable media plugin sandbox for debugging purposes | All |
| MOZ_DISABLE_NPAPI_SANDBOX | Disable 64-bit NPAPI process sandbox | Windows and Mac |
| MOZ_DISABLE_GPU_SANDBOX | Disable GPU process sandbox | Windows |
| MOZ_DISABLE_RDD_SANDBOX | Disable Data Decoder process sandbox | All |
| MOZ_DISABLE_SOCKET_PROCESS_SANDBOX | Disable Socket Process process sandbox | All |
Setting a custom environment in Windows
1) Close Firefox
2) Browser to the location of your Firefox install using Explorer
3) Shift + Right-click in the folder window where firefox.exe is located, select "Open command window here"
4) Add the environment variable(s) you wish to set to your command window -
set MOZ_DISABLE_NPAPI_SANDBOX=1(return)
5) enter firefox.exe and press enter to launch Firefox with your custom environment
Local Build Options
To disable building the sandbox completely build with this in your mozconfig:
ac_add_options --disable-sandbox
To disable just the content sandbox parts:
ac_add_options --disable-content-sandbox
Bug Lists
Priorities
Security/Process Sandboxing Lists
Triage Lists
- Sandboxing Triage List: https://is.gd/ghRoW8
- Lists sandboxing component bugs that are not tracked by a milestone
- Ignores previously triaged into either sb- or sb+
- Ignores meta bugs and bugs with needinfos
- Global Triage List
- Lists any bug in the database with sb?
- Ignores bugs with needinfos
- sb+ triage list
- Previously triaged bugs that have no milestone and no priority set
- sb? needinfos: http://is.gd/dnSyBs
- webrtc specific sandboxing bugs: https://is.gd/c5bAe6
- sb tracking + 'webrtc'
Roadmap
2020 H1 - Main work focus
- Remote Canvas Drawing operations,
- Prerequisite for win32k.sys lockdown.
- Remote Form widget drawing,
- Prerequisite for win32k.sys lockdown.
- Follow-ups in Bug for defaulting it on
- Remote WebGL drawing,
- See also Out-of-process WebGL compositing.
- Follow-ups in Make it shippable bug.
- Sandbox the GPU Process.
- Stalled on non-reproducible field issues.
- Remote Look and Feel + Theming.
- Prerequisite for win32k.sys lockdown.
- Shared memory with read-only and read/write mode.
- Security and memory usage win.
- Use memfd_create for shared memory.
- Performance win and would solve many issues with people running into problems with the default docker/kubernetes configurations that only give a tiny amount of shared memory.
- Enable further telemetry for third-party process injection.
2020 H2 - Main work focus
- Carry-over of win32k.sys lockdown prerequisites from 2020 H1.
- Carry-over of stalled GPU sandboxing work.
- Remaining win32k.sys blockers.
- Enable CIG in RDD.
- Investigate/experiment with feasibility of shipping CIG in content.
Communication
| Weekly Team Meeting | Thursday at 8:00am PT
|
| Matrix |
|
People
| Engineering Management |
|
| Project Management |
|
| QA |
|
| Development Team |
|
Repo Module Ownership
Links
- Electrolysis Wiki Page (lot of additional resource links)
- Security/Sandbox/macOS_Release - description of what to do when a new macOS release comes out in order to find out what updates they made to the sandbox.
- Chromium Sandbox
- Apple's Sandbox guide
- "Introducing Chrome's next-generation Linux sandbox" (seccomp-bpf related)
- Native Client on Wikipedia (Links to papers on Native Client's design and use of SFI, as well as papers on SFI itself.)
- Features of Protected Mode in Internet Explorer
B2G Archive
B2G has always been “sandboxed” to some extent; every app/tab gets its own content process, which uses the Android security model: a separate uid per process, no group memberships, and kernel patches that require group membership for things like network access. But privilege escalation via kernel vulnerabilities is relatively common, so we also use the seccomp-bpf system call filter to reduce the attack surface that a compromised content process can directly access.