Security/Sandbox
Overview
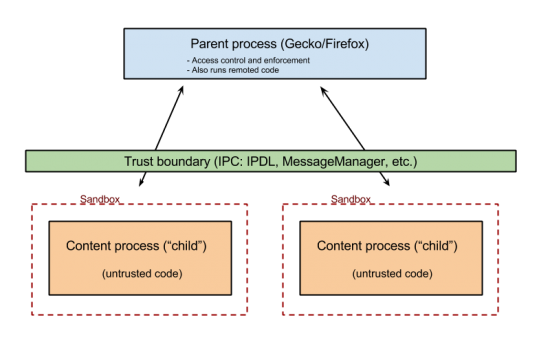
Security Sandboxing makes use of child processes as a security boundary. The process model, i.e. how Firefox is split into various processes and how these processes interact between each other is common to all platforms. For more information see the Electrolysis wiki page. The security aspects of a sandboxed child process are implemented on a per-platform basis. See the Platform Specifics section below for more information.
Current Status
For information on individual milestones visit the Sandboxing Milestones wiki page.
| Sandbox | Trunk | Aurora | Beta | Release |
|---|---|---|---|---|
| Windows (content) | Level 2 | |||
| Windows (GMP) | enabled | enabled | enabled | enabled |
| Windows 64bit (Plugin) | enabled | enabled | enabled | enabled |
| OSX (content) | enabled | |||
| Linux (content) | ||||
| Linux (GMP) | enabled | enabled | enabled | enabled |
DXR search for the current sandbox preferences.
Windows
Content
| Sandbox Feature | Level 0 | Level 1 | Level 2 | Level 10 | Level 20 |
|---|---|---|---|---|---|
| Job Level | JOB_NONE | JOB_NONE | JOB_INTERACTIVE | JOB_RESTRICTED | JOB_LOCKDOWN |
| Access Token Level | USER_NON_ADMIN | USER_NON_ADMIN | USER_INTERACTIVE | USER_LIMITED | USER_LOCKDOWN |
| Alternate Desktop | yes | yes | |||
| Initial Integrity Level | INTEGRITY_LEVEL_MEDIUM | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW |
| Delayed Integrity Level | INTEGRITY_LEVEL_MEDIUM | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_LOW | INTEGRITY_LEVEL_UNTRUSTED |
| Mitigations |
MITIGATION_BOTTOM_UP_ASLR |
MITIGATION_BOTTOM_UP_ASLR |
MITIGATION_BOTTOM_UP_ASLR |
MITIGATION_BOTTOM_UP_ASLR | |
| Delayed Mitigations |
MITIGATION_STRICT_HANDLE_CHECKS |
MITIGATION_STRICT_HANDLE_CHECKS |
MITIGATION_STRICT_HANDLE_CHECKS |
MITIGATION_STRICT_HANDLE_CHECKS |
Gecko Media Plugin
| Sandbox Feature | Level |
|---|---|
| Job Level | JOB_LOCKDOWN |
| Access Token Level | USER_LOCKDOWN |
| Initial Integrity Level | INTEGRITY_LEVEL_LOW |
| Delayed Integrity Level | INTEGRITY_LEVEL_UNTRUSTED |
| Alternate desktop | yes |
| Mitigations |
MITIGATION_BOTTOM_UP_ASLR |
| Delayed Mitigations |
MITIGATION_STRICT_HANDLE_CHECKS |
64-bit Plugin
Released with known issues that break certain Flash features. If you're testing 64-bit builds and come across Flash issues please file a bug.
| Sandbox Feature | Level |
|---|---|
| Job Level | JOB_UNPROTECTED |
| Access Token Level | USER_INTERACTIVE |
| Initial Integrity Level | INTEGRITY_LEVEL_LOW |
| Delayed Integrity Level | INTEGRITY_LEVEL_LOW |
| Alternate desktop | no |
| Mitigations |
MITIGATION_BOTTOM_UP_ASLR |
| Delayed Mitigations |
OSX
TBD
Linux
Content
- Currently not enabled for any build.
- Current goal is to get seccomp-bpf enabled on Nightly with a rather porous filter rule set.
Gecko Media Plugin
- A seccomp-bpf filter is enabled for all builds.
Platform Specifics
Windows
Source Code Overview
The core of the Windows sandbox is Google's chromium sandbox. Relative to the root of mozilla-central, the sandbox exists at:
security/sandbox
The chromium sandbox is based on the chromium base libraries (Google's code) which are located at:
security/sandbox/chromium/base
There is also partial/shim code to get the base code compiling with our SDK build settings or to limit the base code by reducing dependencies at:
security/sandbox/chromium-shim/base
The chromium Windows sandbox itself (Google's code) is located at:
security/sandbox/chromium/sandbox/win
Processes Overview
There are 2 processes when dealing with a sandboxed application:
- The broker: The parent process that starts sandboxed children
- The target: The child process that is sandboxed
Both processes make use of the chromium sandbox library, but they make use of it indirectly through 2 libraries (Mozilla code). This indirect use of the library is due to header conflicts with the ipc layer where it has a different, much older, non compatible, copy of the chromium base library:
- For the broker, ./security/sandbox/win/src/sandboxbroker
- For the target, ./security/sandbox/win/src/sandboxtarget
Build settings
To disable building the sandbox completely build with this in your mozconfig:
ac_add_options --disable-sandbox
To disable just the content sandbox parts:
ac_add_options --disable-content-sandbox
Environment variables
| Disable content process sandbox | MOZ_DISABLE_CONTENT_SANDBOX |
| Disable media plugin sandbox | MOZ_DISABLE_GMP_SANDBOX |
| Disable NPAPI process sandbox | MOZ_DISABLE_NPAPI_SANDBOX |
| Allow weaker than default sandbox level | MOZ_ALLOW_WEAKER_SANDBOX |
| Enable sandbox logging | MOZ_WIN_SANDBOX_LOGGING |
Key source code locations
The sandboxed target process lowers its own privileges after initialization via these calls:
Content process
GMP process
NPAPI process
Level descriptions header:
http://mxr.mozilla.org/mozilla-central/source/security/sandbox/chromium/sandbox/win/src/security_level.h
The call that starts the sandboxed process in Firefox is:
https://dxr.mozilla.org/mozilla-central/rev/918df3a0bc1c/ipc/glue/GeckoChildProcessHost.cpp#1030
All of the code that sets policies can be found here:
http://dxr.mozilla.org/mozilla-central/source/security/sandbox/win/src/sandboxbroker/sandboxBroker.cpp
OSX
TBD
Linux
Most Linux systems have seccomp-bpf, but for limitations that apply to the semantics of system calls (e.g., “can this process access the filesystem”, not “can this process use system call #83”) we require unprivileged user namespaces, which a large minority of desktop Firefoxes don't yet have. Specifically: chroot()ing into a deleted directory to revoke FS access, and namespace unsharing for networking, SysV IPC if possible, and process IDs.
seccomp-bpf filtering rules for various processes:
http://mxr.mozilla.org/mozilla-central/source/security/sandbox/linux/SandboxFilter.cpp
B2G
B2G has always been “sandboxed” to some extent; every app/tab gets its own content process, which uses the Android security model: a separate uid per process, no group memberships, and kernel patches that require group membership for things like network access. But privilege escalation via kernel vulnerabilities is relatively common, so we also use the seccomp-bpf system call filter to reduce the attack surface that a compromised content process can directly access.
Bug Lists
Milestones
- Windows Content Process
- Mac Content Process
- Linux Content Process
- Windows 64-bit NPAPI
Triage Lists
- Triage list: http://is.gd/Mfb8L9
- Lists any bug with sb?
- Lists sandboxing component bugs that are not tracked by a milestone
- Ignores sb+, sb-, and sb? bugs with needinfos
- meta bugs
- sb? Triage List: http://is.gd/B3KscF
- does not include needinfo bugs
- sb? needinfos: http://is.gd/dnSyBs
Tracking Bugs
- Sandboxing Component
- bug 925570 Process sandboxing work
- bug 1011491 Tighten Windows GMP sandbox policies
- bug 1066612 Apply Chromium sandbox "process-level mitigations" to GMP process
- bug 1105816 Tighten Windows content sandbox policy
- bug 1083344 Tighten rules for Mac OS content process sandbox on 10.9 and 10.10
- bug 1149706 Remaining issues for content process sandboxing on the Mac
- bug 1076385 Sandbox the content process on Mac
- bug 1123755 Tighten Windows NPAPI process sandbox policy
- bug 1196384 (sandbox-fs) Deny file system access for content processes
- bug 1124817 Move file access and API usage away from content process
Communication
| Weekly Team Meeting | Thursday at 8:00am PT
|
| IRC |
|
| Newsgroup/Mailing List |
People
| Engineering Management |
|
| Project Management |
|
| QA |
|
| Development Team |
|
| Other Teams |
|
Repo Module Ownership
Links
- Electrolysis Wiki Page (lot of additional resource links)
- Chromium Sandbox
- Apple's Sandbox guide
- "Introducing Chrome's next-generation Linux sandbox" (seccomp-bpf related)
- Native Client on Wikipedia (Links to papers on Native Client's design and use of SFI, as well as papers on SFI itself.)