Security/Reviews/Pancake
NOTE: THIS PAGE WILL BE CONVERTED TO A MEDIA WIKI FORM SOON. DATA CAPTURED HERE WILL BE CONVERTED OVER.
Contents
Status
| Pancake (Firefox Home) | |
|---|---|
| Tracker Bug | Bug 679130 |
| Stage | Definition |
| Status | Red (Green, Yellow, Red?) |
| Release Target | Live |
| Health | - |
| Status Note | |
Team
| Product manager | |
| Feature manager | - |
| Engineering lead | |
| Infrastructure Security lead | Michael Coates |
| Product Security lead | Ian Melven |
| Privacy lead | Sid Stamm |
| Localization lead | - |
| Accessibility lead | - |
| QA lead | Naoki Hirata |
| UX lead | - |
| Product marketing lead | - |
| Additional members | - |
Open issues/risks
Stage 1: Definition
Introduction
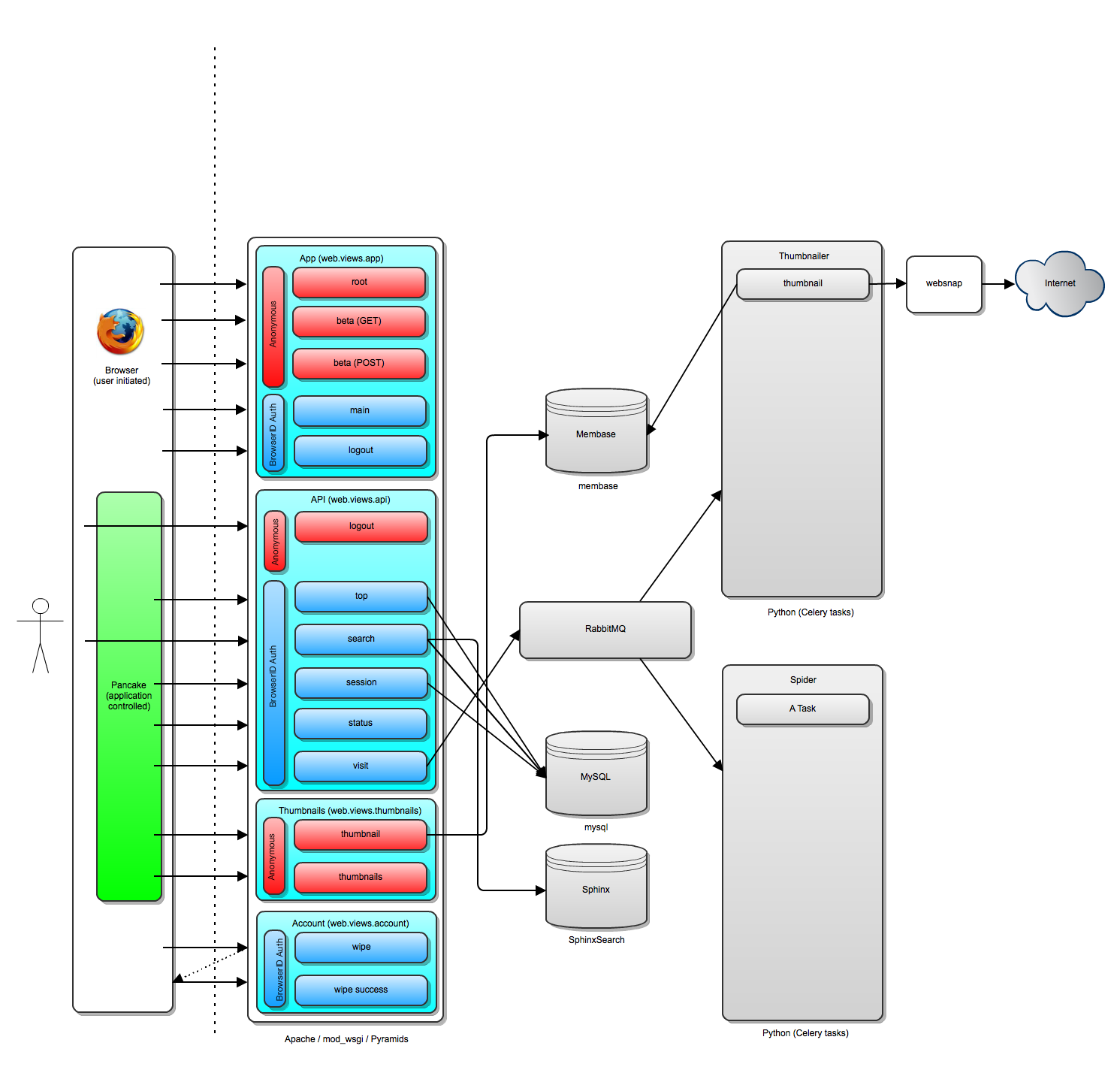
Pancake is the code name for the server side/web service application that will meet demands of firefox home users.
Use Cases
Data Flows
Architecture Diagram
Stage 2: Design
Threat Model
Upload threat model diagram Include links to relevant files, etc, here.
Business Test Cases
Document application specific test cases here
Privacy Risk Analysis
(Status of and link to privacy review and outcome here)
Stage 3: Planning
Application Security Requirements
Document individual requirements for the application here (e.g. CEF logging, captcha, etc)
Operation Security Requirements
Document network/platform security requirements here (e.g. IDS concerns, firewall changes, system hardening reqs, etc)
Mana Website Creation Form
Critical Security Requirements
Itemize individual security blockers here. Reference components in section AppSec or OpSec subsections. These blockers must be addressed before the product can go live.
Stage 4: Development
Repeatable Security Test Cases
Document individual repeatable security test cases here. Include a reference to the source repo, and documentation that governs how to execute test cases.
Secure Coding Guidelines
Document specific secure coding guidelines to be followed and relate them to specific issues/requirements that are specified; capture bug ids related to those issues.
Code Review Milestones
Table 1 - itemized list of code review milestones {i.e. breakdown of specific components that will be reviewed} Table 2 - list of app components/modules that should trigger additional security review (e.g. auth, csrf, file upload handling, etc)
Stage 5: Release
Application Security Verification
These subsections should contain a list of the steps to be taken, and the status of each activity
Code Review
Automated Security Testing
Manual Security Testing
Operational Security Verification
ArcSight Information
Network Design Security Review
Database Security Review
Platform Security (Hardening & Specific Config Requirements)
Landing Criteria
This should be a table itemizing everything from Stage 3 - Critical Security Requirements, including status. For status Red=Unimplemented,Yellow=implemented,Green=tested and passed?
Stage 6: Post Implementation Review
Production Security Considerations
Document additional/ongoing work for this application (e.g. specific things to watch for in ArcSight, gaming behaviour, etc)
Post Implementation Tasks
Itemize process/kb changes developed from this project (e.g. secure coding guidelines, policy stuff, etc)
Team status notes
| status | notes | |
|---|---|---|
| Products | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |
| Engineering | tbd | - |