Security/Projects/Minion
Minion Overview
Minion is an open source Security Automation platform. The 0.3 release of Minion allows Development, QA, and Security team members to perform automated web security scans with a set of tools, and re-execute those scans as needed.
The 0.3 release incorporates significant changes, including a migration away from Django and Bootstrap to a Flask and Angular.js based application. It also involves significant improvements in back-end performance and scaling, and an updated plugin architecture.
This is the first Minion release that is ready for large scale adoption with access management features to constrain which users can access scan results, and an invitation system to actively engage new users.
Minion Principles
Minion should be easy to use.
A user should be able to log into Minion and immediately start to launch scans against sites available to them. Results should be easy to discover and contain detailed explanations.
The target audience for Minion should be developers
Developers should be able to use Minion the moment they have code written that can be tested. The initial focus will be on supporting web applications and services, but this should extend to other applications with the cohort feature set. The initial guidance surfaced by the default reporting engine should be useful, accurate, and actionable by developers, and meaningful to other audiences (QA, Security, Management).
Minion is a platform, not a security tool
Minion is an extensible platform that allows automation of security tasks. As such the focus should be on providing strong abstractions and a reliable, extensible platform without binding the platform to a specific suite of tools. All security testing functionality should be external to Minion and implemented via plugins.
Minion is scalable and extensible
It should be simple to add support for unsupported tools. In addition to the ease with which plugins can be authored, the plugin architecture must isolate plugin related issues from the core platform and allow delegation out to separate infrastructure, and must support scaling from small teams to enterprises that may deliver services to third parties.
Minion is a secure tool
Ongoing security testing and security assessment should be performed on Minion. Major releases and milestones should be accompanied with a detailed explanation of data collected, and risks or threats posed by the tools and plugins that are shipped by the core development team.
Minion is open
Minion is an open source platform, and the core team actively encourages developers, security professionals, and interested parties to provide feedback and feature requests.
Architecture
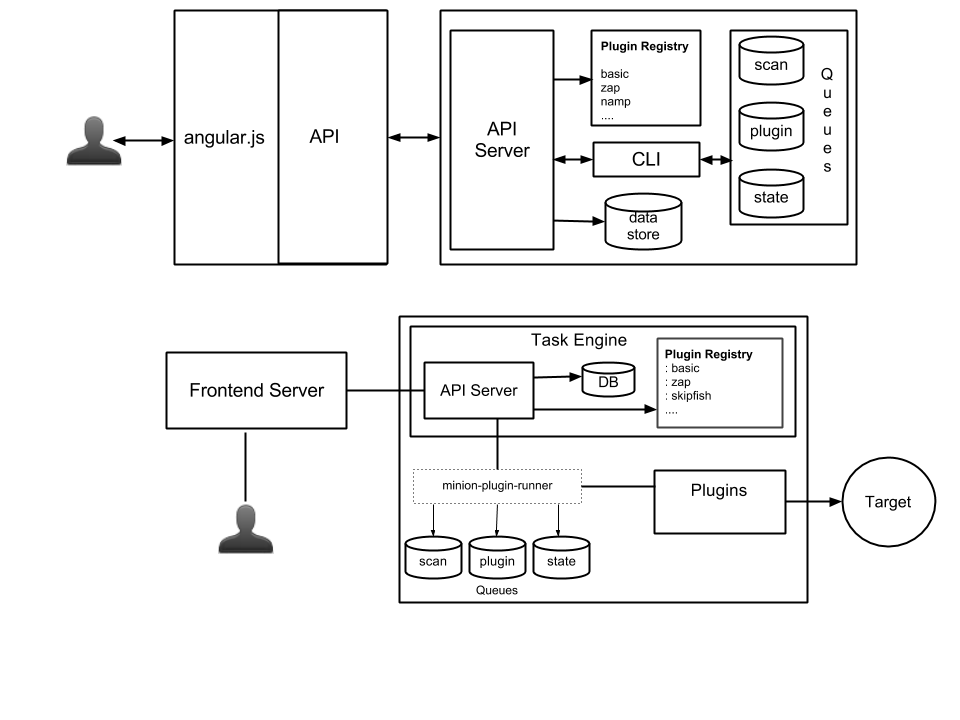
The Minion Front-End is an Angular.js based application that invokes a set of API on the backend. The backend is comprised of a set of services that are collectively referred to as the Task Engine, and a set of plugins. The architecture is designed to be distributed so the plugins can run on any platform that can expose the correct API, ensuring that tools can be incorporated into Minion regardless of operating system dependencies.
Roadmap
Q3 2013
- Site Ownership Verification
- Results Reporting Improvements
Q4 2013
- Reporting Plugins
- Landing Pages
- Deferred Execution Plugins
- Scan Intensity Level
Q1 2014
- Cohort PoC
- Historical Issue Tracking
- Interpolation Engine
- Common Configuration Schema (Extending DEX-JSON)
Wish List
- Site and User Data Privacy
- Minion Event Model Extensions (simple extensibility)
- Scramble - interactive script for generating plugins
Details
This information is preserved from an early iteration of the project. The information is obsolete and in most cases invalid, but the core concepts remain the same.
Links
All of the following are publicly accessible:
- Source code: https://github.com/mozilla/minion
- Email list: http://groups.google.com/group/mozilla-minion-dev
- Security/Projects/Minion/Roadmap
- We also use the #websectools channel on irc.mozilla.org
Minion Virtual Machine
You can find instructions and tools to build a Minion virtual machine on Github.
Developers
You can find most of us on #websectools or on Github.
- April King (april)
- Stefan Arentz (st3fan)
- Simon Bennetts (psiinon)
- Yeuk Hon Wong (yeukhon)
- Matthew Fuller
- Mark Goodwin (mgoodwin)
- Yvan Boily (yvan)
List of plugins
The following projects are optional plugins for minion that add more functionality or wrap existing tools:
https://github.com/mozilla/minion-zap-plugin https://github.com/mozilla/minion-ssl-plugin https://github.com/mozilla/minion-skipfish-plugin https://github.com/mozilla/minion-nmap-plugin https://github.com/mozilla/minion-breach-plugin https://github.com/mozilla/minion-garmr-plugin https://github.com/mozilla/minion-zest-plugin